Access: Fast, Secure Access to Remote Infrastructure
Today, we're incredibly excited to launch Fig Access 🚀🚀🚀
Fig Access makes it ridiculously easy for you (and your team) to connect to SSH servers.
We give you a centralized directory of all of your servers. Connecting is as easy as running fig ssh. See the demo below
To get started, run
fig, go to the Access tab, and import your existing hosts!
If you don't have Fig, download it here or by running brew install fig
Why would I use Fig Access over traditional SSH?
Fig Access offers 5 main value adds over using your ~/.ssh/config:
- ☁️ Cloud-first: Fig stores your SSH servers and credentials securely in the cloud. Add a host once and it's instantly accessible from all your devices.
- 🔒 Secure: Credentials (like secrets and private keys) are encrypted in transit and at rest. No more sending passwords across Slack or email.
- ⚙️ Easy configuration: Fig's UI gives you structure and in-line documentation for things like port-forwarding, jump hosts, and more. No more man pages!
- 🧑💼 Designed for teams: Onboarding a new engineer to your servers is as easy as adding them to your team. No more out of date wikis and copy-paste.
- 🔎 Discoverability: What was that server called again? Fig's centralized directory and ranking algorithms makes it easy to search through thousands of hosts and find the right one quickly.
And all you need to remember is one command: fig ssh!
Why is it called "Access"?
Great question. What we've announced sounds like an SSH client, right?
Well, we obviously have a lot more planned. We are going to expand the product massively along two vectors:
1. Infrastructure
Engineers don't just access servers. They access kubernetes clusters, databases, remote desktops, applications, etc. Why do these all require different protocols and different starting points? We like to think of all of these as "infrastructure". We want accessing all of them to start from one place: Fig.
2. Security
Fig Access shouldn't just be the fastest way of accessing machines, it should also be the most secure.
Today, we support authentication through public/private key pairs. In saying that, we don't think these forms of authentication are as secure they could be. We will save why for another blog post.
Instead, Fig will offer identity-based access. This will allow engineers to authenticate with SSO providers like Okta or GSuite and provide extra layers of security like MFA and biometrics. The most common causes of data breaches are traced to human error, such as stolen, lost, or misconfigured passwords. Identity-based, "zero trust" access managed by short-lived certificates under the hood should reduce any attack risk massively.
Additional FAQ
How does Access manage secrets (like passwords and private keys)?
Fig encrypts secrets in transit and at rest. We are adding support for E2E encryption soon. If you want to wait until that, then you can still use Fig but manage secrets yourself. Simply choose the "Path" authentication method and point to your local private key.
Does Access add/remove public keys from the remote machine?
Not yet. This will come when we enable identity-based access. Fig's certificate authority will provision auto-expiring certificates tied to a user identity to both you and the server.
How can I share hosts across my team?
Easy! Create a new team in Fig. All hosts and identities created under your team's namespace stay in that namespace. Sharing hosts with your teammate is as easy as adding them to that team.
How can I quickly create hosts/servers?
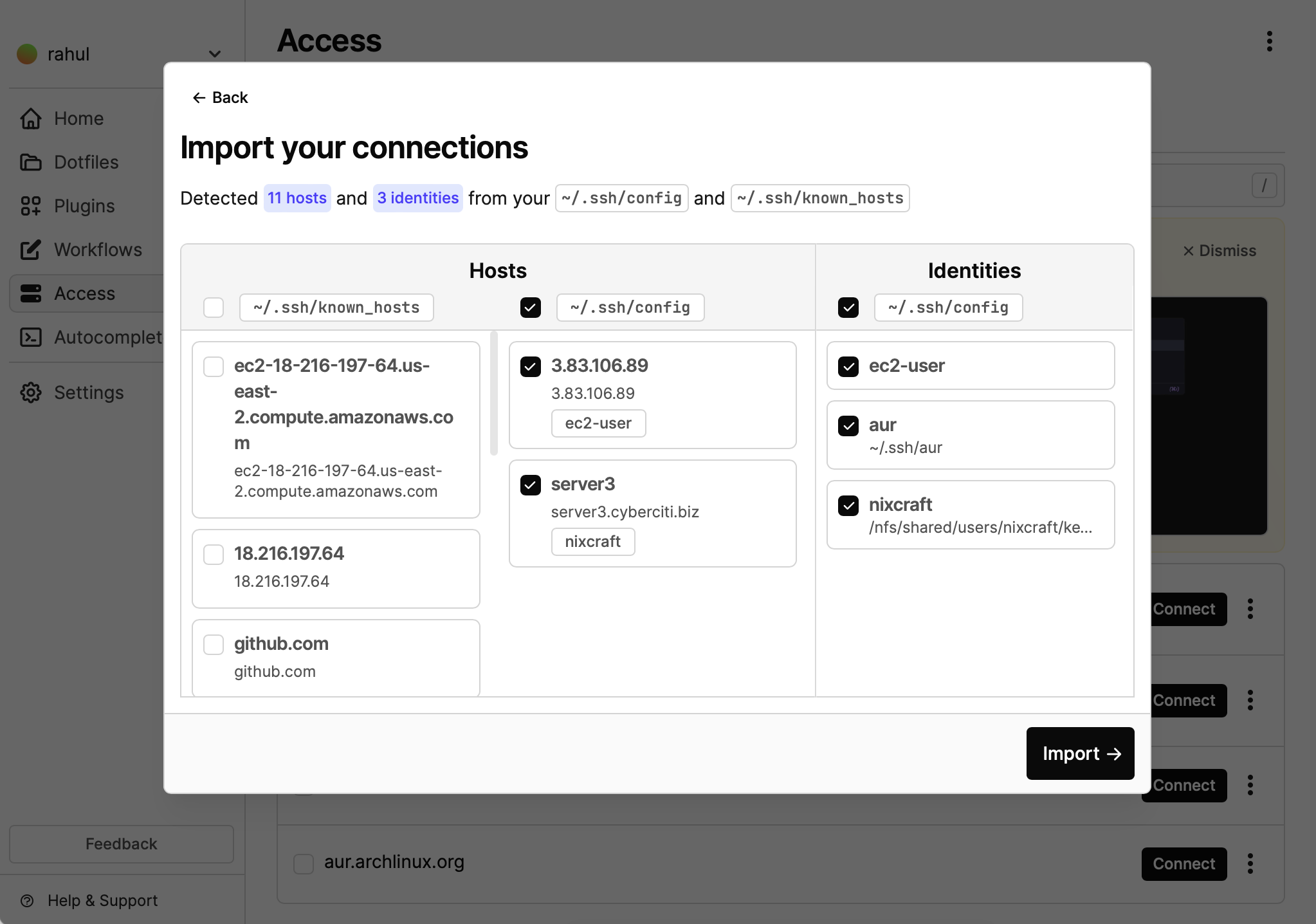
Our built-in importer parses your ~/.ssh/config and ~/known_hosts file and automatically creates hosts and identities for you!
What's next for Access?
Most of this was already discussed above. But to re-emphasize, Fig Access makes it fast and secure to access your remote infrastructure. We're starting with access to SSH servers but will soon enable identity-based access to kubernetes clusters, databases, IoT devices, and more, all from your existing terminal!
To get started, just run fig ssh.
We're excited to launch Access and we are eager to hear your feedback ❤️
Want to stay up to date? Follow us on Twitter: twitter.com/fig